Source Link Privacy.

Tarlogic Security has detected a backdoor in the ESP32, a microcontroller that enables WiFi and Bluetooth connection and is present in millions of mass-market IoT devices. Exploitation of this backdoor would allow hostile actors to conduct impersonation attacks and permanently infect sensitive devices such as mobile phones, computers, smart locks or medical equipment by bypassing code audit controls.
Update: The ESP32 “backdoor” that wasn’t.
And then there is trump, the illegitimate president, Russian stooge, trying to repeal the CHIPS act.
Since when HCI is backdoor ? Someone doesn’t understand how bluetooth works. HCI allows for vendor extensions by design. https://www.bluetooth.com/wp-content/uploads/Files/Specification/HTML/Core-54/out/en/host-controller-interface/host-controller-interface-functional-specification.html
That is a big one. IoT lives off ESP32.

Yeah. We found the thing we were pretty sure was there!
Though, if it’s really just local debug commands, then the usual “malice vs stupidity” debate is still up for grabs.
Well, at least nobody uses that tech. /s
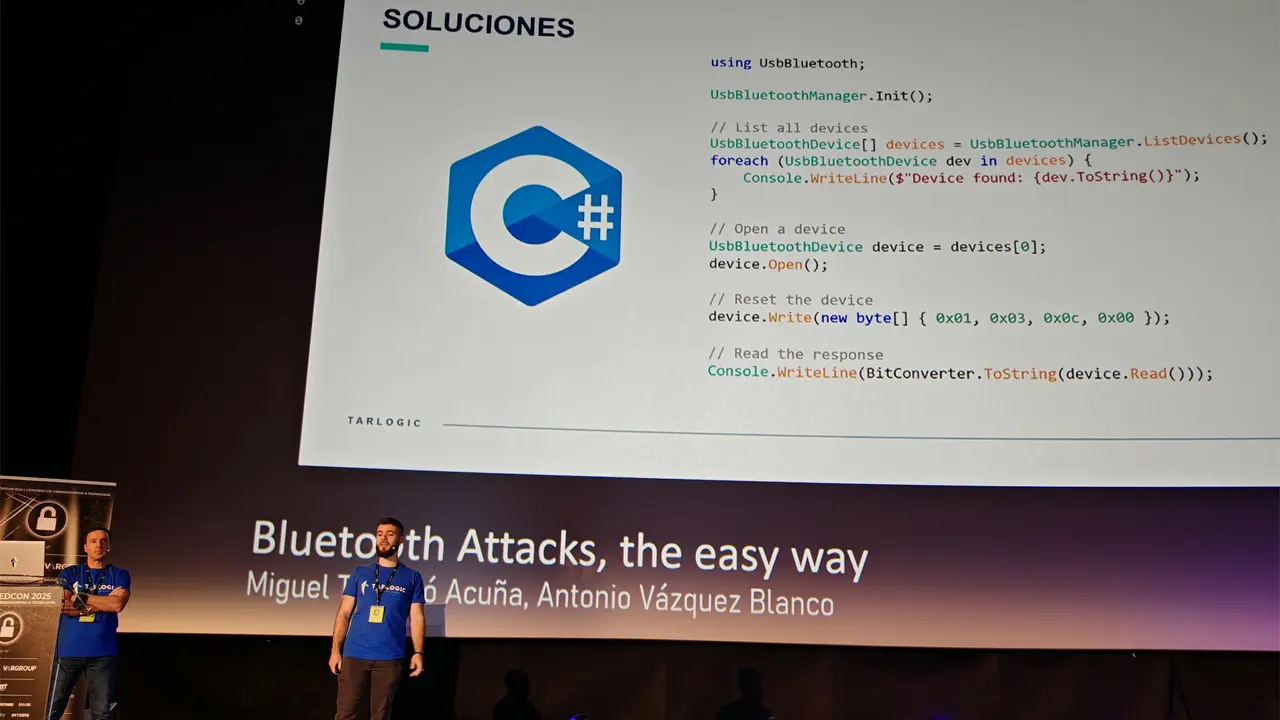
Tarlogic has detected that ESP32 chips, which allow connectivity via WiFi or Bluetooth, have hidden commands not documented by the manufacturer. These commands would allow modifying the chips arbitrarily to unlock additional functionalities, infecting these chips with malicious code, and even carrying out attacks of identity theft of devices.
It’s not a backdoor, it’s a jailbreak. Sounds like they left the debug functionality enabled but just undocumented.
Edit: They’re undocumented HCI commands, that’s the protocol the host (aka CPU) uses to talk to the chip, not a remote device.
Here is hoping this will at least make it easier to take back control of tuya devices